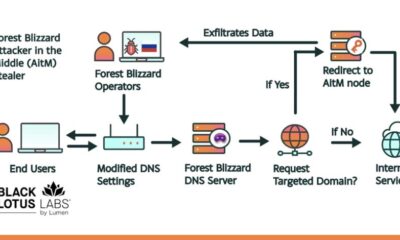
The digital landscape for businesses is a constant game of cat and mouse, where security professionals build ever-higher walls and threat actors search for the smallest crack to slip through. Recent analysis from cybersecurity firms Cisco Talos and Trend Micro has revealed a particularly cunning tactic being used by groups behind the Qilin and Warlock ransomware strains. These attackers are not just writing malicious code; they are weaponizing legitimate, but flawed, software components already on a system to disarm the very tools designed to stop them. This method, known as Bring Your Own Vulnerable Driver (BYOVD), represents a sophisticated escalation in the ongoing cyber war.
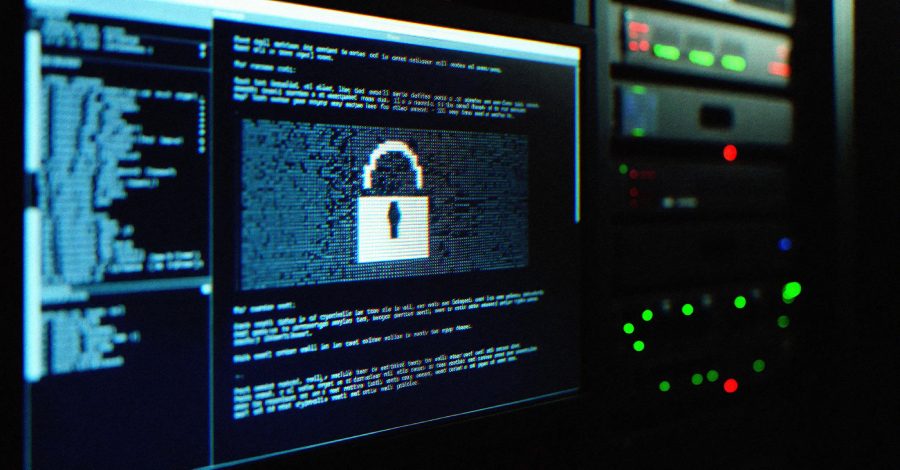
Imagine investing in a state-of-the-art alarm system for your physical store, only for a burglar to arrive with a master key that disables every sensor silently. That is the essence of the BYOVD attack. Instead of trying to hide from Endpoint Detection and Response (EDR) software, which monitors a device for suspicious activity, the attackers bring a driver with known security weaknesses. Once installed or activated, this driver is used to gain high-level access to the computer’s core, the kernel. From that privileged position, disabling over 300 different EDR and antivirus products becomes a trivial task, leaving the system utterly exposed.
Deconstructing the Attack Chain and a Malicious DLL
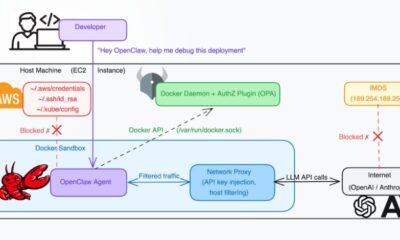
In the specific case of Qilin ransomware operations examined by Talos, the attack chain involves deploying a malicious file named “msimg32.dll.” This name is a classic example of a technique called “DLL side-loading,” where a harmful file masquerades as a legitimate, trusted system library. When a legitimate program tries to load what it thinks is the real msimg32.dll, it inadvertently executes the attacker’s code instead. This provides the initial foothold, a quiet and deceptive entry point that often goes unnoticed by traditional security checks focused on more obvious threats.
This initial compromise is just the beginning. The ultimate goal is to establish kernel-level control, and that is where the vulnerable driver comes in. These drivers are often sourced from legitimate hardware manufacturers but contain unpatched flaws that allow unauthorized kernel access. By exploiting these flaws, the ransomware operators can effectively turn off the digital lights, creating a shadow where their full malicious payload, including file encryption and data theft, can operate without interruption. It is a stark reminder that security is only as strong as its weakest link, and sometimes that link is a trusted piece of software.
The Critical Intersection of Cybersecurity and Domain Reputation
For domain investors, brand managers, and business owners, this news transcends typical IT security alerts. A successful ransomware attack does not just lock files; it can devastate an online brand built over years. Consider a thriving e-commerce site with a memorable, valuable domain name. An attack that takes the site offline for days, leaks customer data, or defaces the homepage causes immediate financial loss and inflicts long-term reputational damage. The trust associated with that domain name, a key component of its intangible value, evaporates.
Your domain is the cornerstone of your digital identity, the address where your reputation lives. A security breach tarnishes that address, making it synonymous with risk and negligence in the minds of customers and partners. Recovery involves more than just restoring data from backups; it requires a concerted public relations effort to rebuild trust. This is why a proactive security posture is not an IT cost but a fundamental brand protection strategy. It safeguards the equity stored in your domain.
Building a Resilient Digital Foundation
So, what can be done? The first line of defense is rigorous patch management. The drivers exploited in BYOVD attacks often have patches available. Ensuring all software, especially low-level drivers, is up-to-date closes many of these doors before attackers can find them. Furthermore, advanced security solutions now offer features like driver allow-listing, which only permits signed, authorized drivers to load, and kernel-level protection that monitors for suspicious driver activity. For businesses, this means moving beyond basic antivirus to layered security strategies.
Your choice of online partners also forms a critical part of your defensive perimeter. Just as you would not build a physical store on unstable ground, you should not build your web presence on a flimsy foundation. Working with a registrar and host that prioritizes security infrastructure, offers clear communication during incidents, and provides tools to help you secure your site is crucial. A trusted, free domain name registrar and web hosting provider like Register it understands that security is integral to maintaining a strong online presence, offering a stable platform from which to grow your brand securely.
Turning Threat Intelligence into Strategic Advantage
Understanding these threats also informs smarter domain investment and development strategies. Savvy domainers might look at industries heavily targeted by ransomware, such as healthcare, legal services, or manufacturing, and consider the defensive branding potential of certain domains. Names that convey security, reliability, and trust could hold increasing value. For developers, building websites with security best practices baked in from the start, such as regular updates, strong access controls, and reliable backups, directly protects the asset value of the domain itself.
The story of Qilin and Warlock is more than a technical bulletin; it is a narrative about the fragility of digital trust. Every business operating online is a potential target, and the consequences of a breach extend far beyond encrypted files. They strike at the heart of your brand’s credibility, which is often encapsulated in your domain name. In an era where attacks are becoming stealthier and more systemic, a holistic view that intertwines cybersecurity, domain management, and brand strategy is no longer optional. It is the essential framework for sustainable digital success.
Looking ahead, the value of a domain name will become increasingly linked to its security history and resilience. Just as a property with a history of floods affects its insurance and value, a domain associated with security incidents may carry a hidden penalty. The future of online branding will belong to those who view their domain not just as a digital address, but as a fortified asset, proactively defended and meticulously maintained to ensure the trust it represents remains unbreakable.