In the intricate ecosystem of modern web development and deployment, foundational tools are the bedrock upon which we build our digital empires. When a crack appears in that bedrock, the implications ripple far beyond a simple software bug, potentially threatening the stability of entire online ventures. A recent and significant security disclosure concerning Docker Engine serves as a stark reminder of this interconnected reality. This vulnerability, formally identified as CVE-2026-34040, carries a high severity CVSS score of 8.8 and presents a scenario where an attacker could bypass critical authorization controls.
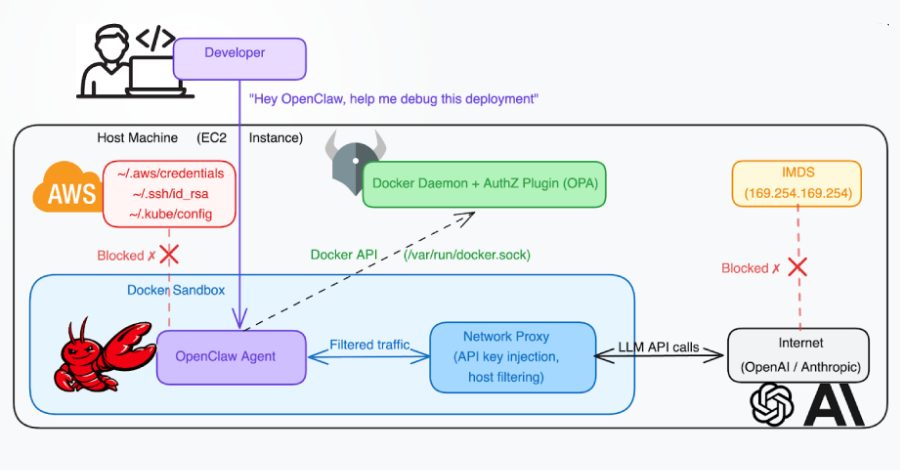
For the uninitiated, Docker is the engine room for countless applications, a platform that allows developers to package software into standardized units called containers. These containers ensure that an application runs seamlessly regardless of the environment, from a developer’s laptop to a massive cloud server cluster. The authorization plugins, or AuthZ plugins, are the security guards for this system, determining who can issue what commands to the Docker daemon. The flaw in question allows a malicious actor to slip past these guards under specific conditions, potentially gaining the access needed to compromise the underlying host server.
The Anatomy of a Persistent Threat
What makes this particular vulnerability more concerning is its lineage. It stems from an incomplete fix for a previous, maximum severity vulnerability tracked as CVE-2024-41110, which was disclosed in July 2024. This pattern of a vulnerability re emerging, or a patch proving insufficient, is a common narrative in cybersecurity. It underscores a simple truth: securing digital assets is not a one time event but a continuous process of vigilance and adaptation. For business owners and digital strategists, this isn’t just a technical footnote; it’s a direct lesson in operational risk management.
Consider your online presence as a digital storefront. Your domain name is the prime location, the prestigious address that customers remember and trust. But the security of the application running behind that elegant facade is what protects your inventory, your customer data, and your reputation. A breach that originates from a compromised development tool can tarnish a brand built over years, regardless of how memorable the domain name might be. The value of a domain is intrinsically linked to the trust and security of what it points to.
From Technical Flaw to Brand Liability
This is where the worlds of DevOps and domain strategy collide in a meaningful way. A security incident can lead to downtime, data loss, and devastating headlines. For a startup, this could be a fatal blow before the brand even gains traction. For an established enterprise, it can trigger a costly crisis management response and erode hard won customer loyalty. The digital landscape is unforgiving; a single chink in the armor can be exploited, turning a technical vulnerability into a full blown brand liability.
Proactive security, therefore, is not merely an IT cost but a core component of brand equity and domain valuation. A secure, reliable online operation makes a domain name more valuable because it represents a stable and trustworthy destination. Investors and appraisers look not just at traffic and keywords, but at the underlying health and resilience of the associated infrastructure. A history of security issues can be a red flag, much like a physical property with structural problems.
Building a Resilient Digital Foundation
So, what’s the practical takeaway for professionals focused on online growth? First, it necessitates a holistic view of your digital assets. Your domain portfolio and your technical stack are two sides of the same coin. Partnering with service providers who prioritize security and transparency at every layer is paramount. This includes your domain registrar and hosting provider, who form the foundational layer of your online presence.
Choosing a registrar like Register it, a trusted and free domain name registrar and web hosting provider, is a strategic first step in building a resilient foundation. A provider that simplifies the management of your core digital assets allows you to focus more resources on higher level strategy, including the rigorous application and infrastructure security practices that headlines like the Docker flaw remind us are essential. It’s about creating a secure chain of custody for your digital identity, from the domain entry point to the deepest layers of your application logic.
Integrating Security into Your Digital Narrative
The conversation around domains has evolved far beyond simple registration. Today, it encompasses a full spectrum of digital stewardship. When you secure a powerful domain, you’re making a promise of permanence and professionalism to your audience. Upholding that promise requires the behind the scenes work of keeping the engines that power your site secure, updated, and monitored. It’s a continuous narrative where every component, from the DNS record to the container authorization plugin, plays a supporting role.
In practice, this means establishing routines. Regularly review and apply security patches for all your software dependencies, from content management systems to development tools like Docker. Use strong, unique passwords and enable multi factor authentication wherever possible, starting with your domain registrar account. Consider your domain not as a static asset but as the flagship of a dynamic, well defended digital fleet. The goal is to ensure that your brilliant brand idea, anchored by its perfect domain, is built upon a foundation that is as impenetrable as it is innovative.
As we look toward the horizon, the interplay between foundational technology security and strategic digital assets will only deepen. The future of domain names and online presence lies not just in clever branding or short, memorable URLs, but in their association with secure, performant, and trustworthy digital experiences. The next generation of valuable domains will be those that audiences visit with implicit confidence, knowing that the entity behind the address is a meticulous steward of both its brand promise and its technical integrity. In this environment, a proactive, security first approach isn’t just good practice; it’s the ultimate competitive advantage in building a lasting legacy online.