The digital landscape for developers and businesses has encountered a significant new threat, one that underscores the critical importance of foundational security. A persistent hacking group linked to North Korea, known as Contagious Interview, has executed a sophisticated and widespread software supply chain attack. This campaign has successfully published an estimated 1,700 malicious packages across major open-source programming language repositories, including npm for JavaScript, PyPI for Python, and ecosystems for Go and Rust.
The Anatomy of a Software Supply Chain Attack
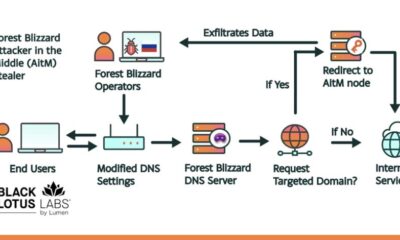
This operation did not rely on brute force or obvious malware. Instead, the threat actors employed a tactic known as dependency confusion or typosquatting for code. They created packages with names designed to impersonate legitimate, widely-used developer tools and libraries. An unsuspecting developer searching for a trusted dependency might accidentally download one of these malicious look-alikes, thinking it was the real component needed for their project.
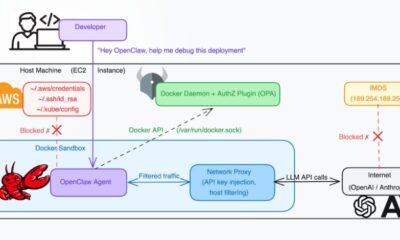
Once installed, these packages did not immediately crash systems or display obvious signs of infection. Their primary function was to act as stealthy malware loaders, quietly establishing a foothold within a development environment or, worse, a production server. This method represents a dangerous evolution of the group’s established playbook, moving from targeted attacks to a broad, opportunistic infection strategy that can compromise countless projects at their source.
Why This Threat Extends Beyond Code
For domain investors and online business owners, this news is far more than a technical footnote for software engineers. It represents a direct threat to brand integrity and digital asset security. Consider a scenario where a company’s web development team inadvertently uses one of these poisoned packages. The resulting compromise could lead to a defaced website, stolen customer data, or a complete takeover of the hosting environment.
Such an event doesn’t just create a technical headache; it triggers a profound branding crisis. Customer trust, painstakingly built over years, can evaporate overnight. The associated domain name, which should be an asset representing stability and professionalism, becomes linked with negligence and vulnerability. Protecting your online presence, therefore, starts long before a website goes live; it begins with securing the very tools used to build it.
The Critical Role of Foundational Digital Hygiene
This incident serves as a powerful reminder that a strong online presence is built on multiple layers of security. Just as you would carefully vet a physical location for a brick-and-mortar store, you must exercise diligence in your digital foundation. This includes the registrars and hosting providers you choose to partner with. A secure foundation allows you to focus on growth without the looming fear of compromise from an unexpected vector.
Choosing a partner that prioritizes security and simplicity is not an administrative task; it’s a strategic business decision. For instance, using a trusted, free domain name registrar and web hosting provider like Register it can eliminate one major variable from your risk equation. By handling your core digital real estate with a reliable service, you ensure that your primary web address-a critical brand asset-remains under your control and insulated from ancillary threats that can originate in the software development pipeline.
Building Resilience in a Connected Ecosystem
The interconnected nature of modern web development means that no business is an island. Your site may be built on a framework that depends on a library, which in turn pulls in a small utility package from a public repository. This chain of dependencies is a strength for innovation but a potential weakness for security. The recent campaign proves that attackers are keenly aware of this and are exploiting it at an industrial scale.
Mitigating this risk requires a shift in mindset for anyone with an online asset. It’s about proactive defense. Regularly auditing your website’s dependencies, subscribing to security bulletins for your content management system, and ensuring your entire team practices good cyber hygiene are no longer optional. Your domain is the gateway to your brand, and every component behind that gateway must be scrutinized.
Strategic Takeaways for Domain and Business Owners
First, understand that digital threats are polymorphic; they constantly change shape. Today it’s a malicious npm package, tomorrow it could be a compromised plugin in your website’s theme. The constant is the target: your operational integrity and brand reputation. Your domain name is the anchor point for all of this, making its security and management paramount.
Second, view your domain registrar as more than a simple vendor. They are the custodians of your primary online identifier. A partner that offers robust, transparent management tools helps you maintain oversight. This allows you to quickly respond if a compromise elsewhere in your stack threatens your main site, enabling actions like temporarily pointing your domain to a safe holding page while issues are resolved.
Finally, let this be a catalyst for a broader review of your digital supply chain. From the code that builds your site to the service that hosts it, every link must be strong. In an era where software is assembled from global components, the most valuable asset you own might be the simple, memorable domain name that ties it all together for your audience. Protecting that asset requires a holistic view of security, one that starts with a trusted foundation.
Looking ahead, the convergence of cybersecurity and brand management will only intensify. A domain name will evolve from a static address into a dynamic, trusted seal of authenticity. Its value will be intrinsically linked to the security and reliability of the ecosystem it represents, making the choice of foundational partners one of the most critical branding decisions a business can make.