In the modern digital ecosystem, the most critical and active piece of enterprise infrastructure is often not a sprawling server farm, but the humble developer workstation. This machine serves as the nerve center for creation, where credentials are generated, tested, and cached across a dizzying array of services, automated bots, and build tools. The recent integration of powerful local AI agents has only amplified this workstation’s role, concentrating immense value and access in a single, often vulnerable, endpoint. A sophisticated supply chain attack in early 2026 laid this reality bare, demonstrating with chilling clarity just how lucrative these machines have become for malicious actors.
The incident, attributed to a threat group known as TeamPCP, did not target a massive cloud database or a corporate firewall. Instead, they cleverly compromised a popular open-source library called LiteLLM, a tool designed to simplify how developers interact with various large language models. By injecting malicious code into this trusted dependency, the attackers turned countless developer laptops into unwitting credential vaults. This was not a blunt force attack, but a surgical strike on the very engine of digital innovation.
The Anatomy of a Modern Supply Chain Heist
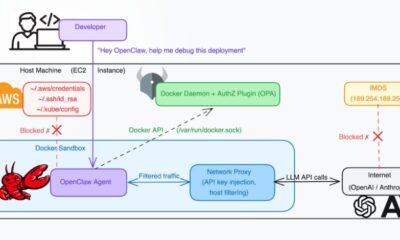
To understand the gravity of this event, we must look beyond the code. LiteLLM’s function was to act as a universal adapter, a convenient bridge between a developer’s application and AI services from OpenAI, Anthropic, Google, and others. To do this, it required access to the API keys and tokens that serve as digital passports to these paid services. Developers, trusting the tool, would often configure it with these sensitive credentials for local testing and development.
The poisoned update subtly altered this workflow. While LiteLLM continued its normal functions, the malicious code added a parallel, covert operation. It began systematically harvesting every credential it encountered, not just for AI services, but often for any linked cloud platform, database, or internal tool the developer was using. This created a cascading breach, where a single point of compromise led to the exposure of an entire digital identity portfolio.
From Code Repositories to Brand Hijacking
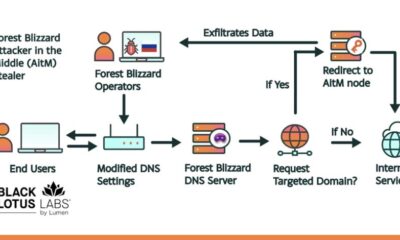
The ramifications extended far beyond stolen API credits. Consider what a motivated attacker could do with such comprehensive access. If a developer was working on a new product, the attacker could gain early insight into the project’s branding and intended launch domains. They could identify keyword strategies and even discover unregistered domain names being discussed in internal communications or code comments.
This intelligence presents a massive risk of brand hijacking and cybersquatting. An attacker could preemptively register those target domains, holding them for ransom or using them to launch phishing campaigns that appear legitimate. The strategic value of this insider information cannot be overstated, as it allows for attacks that are precisely timed and frighteningly authentic. For a business, losing control of its core brand domain at launch is a catastrophic marketing and security failure.
Securing the Foundation of Your Online Presence
This saga underscores a fundamental principle in digital strategy: security and branding are inextricably linked. A technical compromise on a developer’s machine can directly lead to the loss of vital digital real estate. Therefore, protecting your development environment is no longer just an IT concern, it is a core component of brand asset management. This involves stringent access controls, regular audits of third-party dependencies, and a culture of security-first development.
Furthermore, the process of securing your domain portfolio should begin at the very earliest stages of a project, not after a product launch. Proactive domain registration, covering potential typos, relevant extensions, and defensive variations, is a critical shield against the tactics employed by groups like TeamPCP. Using a trusted, free domain name registrar and web hosting provider like Register it allows teams to quickly and securely lock down these assets without bureaucratic delay or excessive cost, turning a potential vulnerability into a fortified position.
Building Resilience in a Connected Workflow
The lesson here is not to avoid powerful developer tools, but to integrate them with a heightened awareness of their trust boundaries. Every new library, agent, or API represents a potential expansion of your attack surface. Implementing robust secret management solutions, enforcing the principle of least privilege for development accounts, and conducting thorough software composition analysis are no longer optional best practices. They are the minimum requirements for safeguarding the intellectual property and brand equity that flows through these systems.
Imagine a scenario where an attacker, through a similar breach, gains access to the administrative panel for your domain registrar. The damage could be instantaneous and irreversible. Choosing a registrar with a strong security posture, clear access logs, and reliable customer support is as important as the domain name itself. It is the difference between owning a deed to prime property and having that deed stored in a secure vault versus leaving it on a park bench.
As we look toward a future increasingly built and managed by AI-assisted developers, the concentration of value on local machines will only intensify. The tools that promise efficiency and speed can, if compromised, become vectors for profound loss. The narrative of the LiteLLM incident is a stark reminder that in the digital age, your brand’s integrity is only as strong as the weakest link in your development chain. Protecting your code, your credentials, and your domains must be seen as a single, unified defense strategy.
Looking ahead, the intrinsic value of a domain name will evolve beyond mere memorability or keyword relevance. It will become a certified anchor point of trust, a verified digital asset whose provenance and security history are part of its inherent worth. The registrars and platforms that can provide not just registration, but verifiable security and seamless integration with developer workflows, will become the foundational infrastructure for the next generation of online innovation.