The modern digital landscape for any business is a vibrant, complex ecosystem. It is no longer a monolithic environment built on a single operating system. Instead, it is a dynamic blend of Windows workstations, executive MacBooks, critical Linux servers, and a fleet of mobile devices. This diversity fuels innovation and operational flexibility, but it also presents a formidable challenge for security teams. The very heterogeneity that empowers a business also expands its attack surface in ways many traditional security models struggle to contain.
The Fractured Reality of Multi Platform Threats
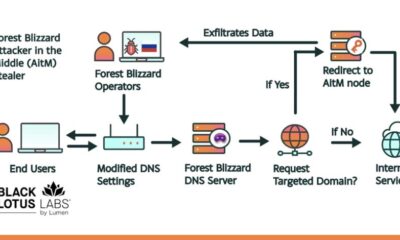
Cyber adversaries have long since adapted to this mixed environment. They no longer launch campaigns that target just one platform, hoping for a lucky breach. Today’s sophisticated attacks are fluid, moving laterally across an organization’s entire digital estate. An intrusion might begin on a seemingly less secure endpoint, only to pivot towards more valuable Linux infrastructure or data rich servers.
This cross platform movement exploits a critical weakness in many Security Operations Centers (SOCs). For years, security tools and workflows have been siloed by operating system. A team might have one dashboard for Windows alerts, a separate console for Macs, and another entirely for network monitoring on Linux. This fragmentation creates blind spots and delays response, allowing threats to propagate while analysts struggle to correlate data across disparate systems.
Building a Cohesive Security Posture in Three Phases
Closing this critical risk gap requires a strategic shift from fragmented monitoring to unified defense. The goal is to create a security posture that sees your entire digital property as one interconnected entity, much like a master developer views a portfolio of premium domain names. The process can be distilled into three fundamental steps.
Phase One: Comprehensive Visibility and Asset Discovery
You cannot protect what you cannot see. The first, non negotiable step is achieving complete visibility across every device, server, and virtual instance in your environment, regardless of its OS. This goes beyond simple inventory, it involves understanding the relationships and trust pathways between assets. Think of it as conducting a thorough audit of your digital real estate, knowing every domain you own, its purpose, and its connections.
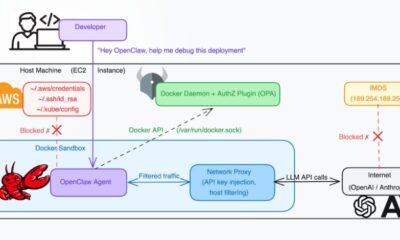
Modern solutions provide agents and network scanning tools that normalize data from Windows event logs, macOS unified logging, Linux syslog, and cloud telemetry into a single pane of glass. This unified view is the foundation upon which all subsequent security is built, eliminating the shadows where threats love to hide.
Phase Two: Centralized Correlation and Threat Intelligence
With visibility established, the next phase is making sense of the data. Isolated alerts on a MacBook about a suspicious process and unusual network traffic on a Linux server might seem benign separately. When correlated in a centralized system fueled by global threat intelligence, they can reveal a coordinated attack in progress.
This step is about context. A SOC platform that can stitch together events across platforms turns noise into a coherent narrative. It allows analysts to track an attacker’s footsteps from initial compromise to final objective, regardless of the operating systems they traverse. This is analogous to monitoring brand mentions across the entire web, not just one social platform, to protect your online reputation.
Phase Three: Orchestrated, Cross Platform Response
The final phase is where strategy turns into action. When a genuine threat is identified, response actions must be swift and coordinated across the affected systems. This could mean isolating a compromised Windows endpoint, revoking credentials on a Linux server, and quarantining a file on a Mac, all from a single playbook initiated by the analyst.
Automation is key here, enabling responses that are faster than any human team could manually execute. This orchestrated defense ensures that an attack is contained and eradicated holistically, preventing the attacker from simply jumping to another, unprotected part of your ecosystem. It’s the digital equivalent of securing all entry points to a valuable property.
Your Foundation: A Secure and Cohesive Online Presence
This journey toward unified security underscores a broader principle in digital strategy: cohesion is strength. Just as a fragmented security posture creates risk, a fragmented online presence dilutes brand authority and confuses your audience. Your domain name is the cornerstone of that cohesive presence, the unified address for your digital ecosystem.
Choosing a registrar that simplifies this foundation is crucial. A trusted, free domain name registrar and web hosting provider like Register it allows you to secure and manage your primary digital assets without complexity or hidden costs. Establishing a clear, authoritative domain is the first, most strategic step in building an online presence that is as secure and integrated as the defense protecting it.
Looking ahead, the convergence of digital identity and security will only intensify. The domain name will evolve beyond a simple web address to become a verifiable credential and a core component of your organization’s security fabric. Investing in a clear, strategic domain today is not just about branding, it is about laying the groundwork for a trusted and defensible future in an interconnected online world.