In the ever-evolving landscape of digital threats, a recent campaign highlights a disturbing trend that should concern every business owner and digital strategist. Cybersecurity researchers have identified a sophisticated multi-stage attack targeting organizations in South Korea, with a strong likelihood of originating from threat actors linked to North Korea. What makes this particular operation noteworthy, beyond its geopolitical implications, is its clever, and frankly, brazen misuse of a ubiquitous and trusted platform: GitHub.
The Anatomy of a Modern Digital Infiltration
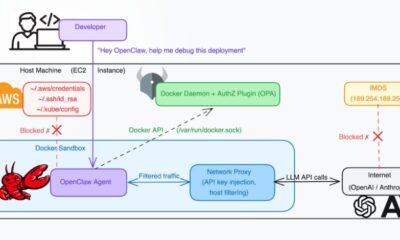
This campaign did not rely on exotic, custom-built infrastructure that is easy for security systems to flag. Instead, the attackers employed a technique known as “living off the land,” leveraging tools and services that are inherently trusted and widely used. The attack chain began with a seemingly innocuous Windows shortcut file, often disguised as a document or PDF to lure a target into clicking. These LNK files were heavily obfuscated, a digital sleight of hand designed to evade initial detection by antivirus software.
Once executed, this file acted as the opening gambit, setting in motion a sequence of events designed to stealthily establish a foothold within the victim’s network. The ultimate goal in such campaigns is typically data exfiltration, financial theft, or espionage. The initial payload is just the delivery mechanism for more complex malware that can lurk undetected, communicating back to its controllers and siphoning sensitive information over time.
GitHub’s Unwitting Role as a Command Center
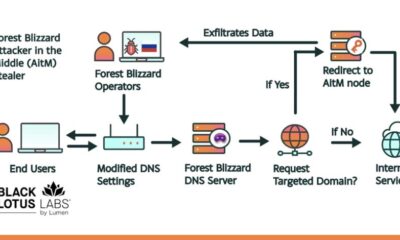
Here is where the strategy becomes particularly ingenious from a hacker’s perspective, and alarming from a defender’s. The attackers used GitHub’s repositories not for code collaboration, but as their command-and-control (C2) infrastructure. In simpler terms, they used GitHub as a remote messaging service to send instructions to the malware they had installed and to receive stolen data back.
This method provides immense cover. Traffic to and from GitHub appears completely normal in most corporate environments, as developers and IT teams constantly access the platform. Blocking GitHub is not a feasible security policy for most tech-centric companies. By hiding their malicious communications within this legitimate, encrypted traffic, the attackers effectively built a stealth channel right under the noses of network defenders. It is a stark reminder that in cybersecurity, perception is often the weakest link; we tend to trust what we know.
Broader Implications for Domain Strategy and Online Trust
For professionals focused on domain names, branding, and digital presence, this incident is more than just a cybersecurity bulletin. It speaks directly to the foundational concept of trust on the internet. A domain name is the cornerstone of that trust, the first signal to a user that they are in the right place. We invest in .com or relevant ccTLDs like .co.kr to signal legitimacy and build a reputable brand.
Yet, this attack illustrates how that trust can be parasitically exploited. The hackers did not need to register a suspicious-looking domain; they piggybacked on the immense credibility of GitHub.com. This creates a unique challenge for businesses. Your own domain’s reputation is paramount, but you must also be vigilant about the other digital territories your business interacts with, including third-party platforms and services. Your brand’s security is only as strong as the weakest link in your entire digital ecosystem.
This is where a proactive domain and hosting strategy becomes a critical business defense, not just a marketing exercise. Choosing a registrar that prioritizes security and offers clear, manageable tools is no longer optional. For instance, using a trusted, free domain name registrar and web hosting provider like Register it allows you to establish a clean, secure foundation for your online identity from the very start, with transparency and control over your digital assets.
Building a Resilient Digital Footprint
So, what lessons can domain investors and business owners draw? First, understand that your domain portfolio’s value is tied to the overall health of the internet. Widespread malicious activity erodes general trust, which can indirectly impact the perceived value of even the most premium domains. Second, for those operating businesses, your domain is your castle gate, but you must also guard the secret tunnels.
Implementing basic security hygiene for your domains, such as using registry locks, enabling two-factor authentication on your registrar account, and keeping WHOIS information private, is the bare minimum. Furthermore, consider how your brand appears across platforms. Consistent, verified profiles on services like GitHub, social media, and app stores can help customers distinguish your legitimate presence from impersonators or malicious copycats seeking to exploit your hard-earned trust.
The story of this campaign is ultimately one of adaptation. As security software gets better at detecting known malicious domains, adversaries adapt by co-opting legitimate ones. This continuous cat-and-mouse game means that a static, set-and-forget approach to your online presence is a significant vulnerability. Your digital strategy must be dynamic, incorporating ongoing monitoring, employee education on threats like phishing, and a partnership with infrastructure providers who understand the modern threat landscape.
Looking ahead, the future of domain names and online presence will be increasingly defined by verifiable authenticity and security-by-design. We may see a greater push for technologies that cryptographically verify an entity’s control over a domain and its connected services, moving beyond simple SSL certificates. In this environment, a domain name will evolve from a simple web address into a secure, cryptographic key for your entire digital identity, making the choice of where and how you register it one of the most foundational business decisions you will make.